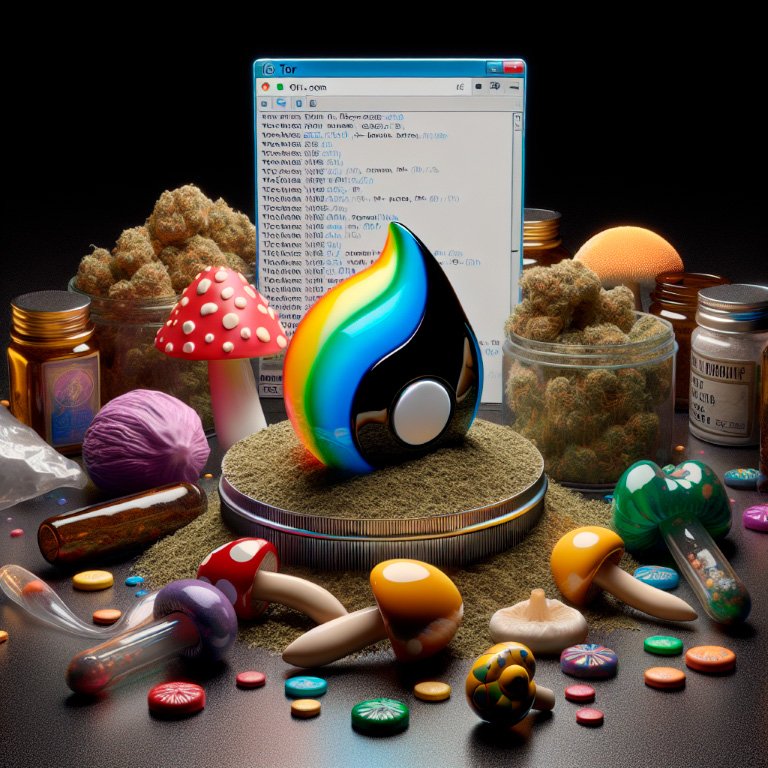
Darknet Markets 2026:
The dark web is part of the deep web but is built on darknets: overlay networks that sit on the internet but which can't be accessed without special tools or software like Tor. Tor is an anonymizing software tool that stands for The Onion Router — you can use the Tor network via Tor Browser.
| Darknet Market | Established | Total Listings | Link |
|---|---|---|---|
| Nexus Market | 2024 | 600+ | Onion Link |
| Abacus Market | 2022 | 100+ | Onion Link |
| Ares | 2026 | 100+ | Onion Link |
| Cocorico | 2023 | 110+ | Onion Link |
| BlackSprut | 2023 | 300+ | Onion Link |
| Mega | 2016 | 400+ | Onion Link |
Updated 2026-06-09
Secure Shopping on the Darknet
The darknet has evolved into a sophisticated e-commerce ecosystem, fundamentally built on the principle of transactional security. This environment leverages advanced encryption technologies to create a secure shopping platform where user identity and financial data are protected from exposure. The foundation of this security is the use of cryptocurrency, which facilitates private and irreversible transactions, effectively severing the traditional link between a purchase and an individual's personal banking information.
This operational framework supports a thriving marketplace where a wide range of products are available through detailed listings. The system is regulated by a robust feedback mechanism, where vendor reviews and ratings provide a transparent record of reliability and product quality. This peer-review process empowers buyers to make informed choices, fostering a self-policing economy based on trust and reputation. The combination of cryptographic anonymity and community-driven accountability ensures a secure and efficient commercial experience for all participants.
How Encryption Keeps Your Darknet Shopping Private
Encryption is the fundamental technology that enables secure and private transactions on the darknet. It functions by scrambling data into an unreadable format during transmission, which can only be deciphered by the intended recipient possessing the correct cryptographic key. This process ensures that all communications, including order details and shipping information, remain confidential and shielded from unauthorized interception.
For participants in darknet commerce, this creates a protected environment where personal identity and transactional data are secured. The use of public-key cryptography is standard, where vendors maintain a public key for encryption and a private key for decryption. This system allows buyers to send encrypted messages that only the specific vendor can open, effectively preventing any third party from accessing sensitive content.
The practical outcome is a marketplace where individuals can engage in trade with a significantly reduced risk of exposure. The assurance of encrypted communications fosters trust and facilitates a thriving economic ecosystem built on the principle of transactional privacy.
Private Crypto Shopping on the Darknet
Cryptocurrency is the financial backbone of the darknet, enabling transactions that are both private and secure by design. Unlike traditional banking, which ties payments to personal identities, cryptocurrencies like Bitcoin and Monero operate on a decentralized ledger. This system records transactions on a public blockchain but uses cryptographic keys to keep wallet addresses pseudonymous, effectively severing the direct link between a financial exchange and a user's real-world identity.
The process is enhanced by the use of tumbling services and coin mixers, which further obfuscate the trail of funds by pooling and redistributing them, making financial tracking exceptionally difficult. This level of transactional privacy is fundamental, as it allows individuals to engage in commerce without fear of their personal financial data being exposed or monitored.
For the darknet economy, this means that buyers can acquire goods with a high degree of confidence in their financial anonymity. The entire purchasing process, from selecting a product to finalizing payment, is shielded by layers of encryption and cryptographic verification, ensuring that privacy is maintained from initiation to completion.
Clear Product Info for Safer Shopping
The darknet hosts a sophisticated e-commerce ecosystem where product variety and information transparency are paramount. Marketplaces offer an extensive catalog of goods, with listings that function like those on conventional online retail platforms. Each product page provides comprehensive details, including high-resolution photographs, precise weight measurements, chemical composition analysis, and country of origin.
This level of detailed product information is critical for consumer safety and informed decision-making. Vendors compete on quality and service, which incentivizes the provision of accurate and thorough listings to build trust and secure positive feedback. The system operates on a foundation of verified customer reviews and vendor ratings, creating a self-regulating environment where quality and reliability are consistently rewarded.
Finding Good Vendors with Reviews
Vendor reviews are the cornerstone of trust and quality assurance within darknet commerce. These user-generated feedback systems transform anonymous transactions into reliable exchanges by providing a transparent record of a vendor's performance. A seller's reputation, built over numerous successful transactions, becomes their most valuable asset, directly influencing their visibility and sales volume.
Prospective buyers rely on this feedback to assess critical factors before purchasing:
- Product quality: Reviews detail the accuracy of the product description versus the item received.
- Shipping speed and stealth: Users report on delivery times and the effectiveness of packaging methods.
- Communication: Feedback highlights the vendor's responsiveness and professionalism in resolving issues.
This system creates a self-regulating environment where high-quality vendors thrive and unreliable actors are quickly identified and marginalized. The cumulative review score acts as a powerful metric, enabling informed decision-making and fostering a competitive marketplace where excellence is consistently rewarded.

How Anonymity Makes Buying on the Darknet Safe
The operational security of darknet commerce is fundamentally dependent on a multi-layered anonymity framework. This system begins with the Tor network, which encrypts and routes user traffic through a series of volunteer-operated servers, effectively obscuring the origin and destination of any connection. This prevents outside observers from determining a user's physical location or the specific sites they are visiting.
Complementing this network-level protection is the mandatory use of end-to-end encryption for all communications. Buyers and sellers interact through encrypted messaging systems where only the intended recipient can decipher the content. This ensures that sensitive information, such as delivery addresses or order specifics, remains confidential and inaccessible to any intermediaries.
Financial privacy is achieved through the exclusive use of cryptocurrencies like Bitcoin or Monero. Transactions are recorded on a public ledger but are designed to be pseudonymous, breaking the direct link between a user's real-world identity and their financial activity on the platform. For enhanced security, users employ tumbling services or built-in wallet features that further obfuscate the transaction trail.
This combination of technologies creates a secure environment where commerce can proceed based on merit and proven trustworthiness, as evidenced by detailed vendor reviews, rather than relying on potentially vulnerable personal identifiers.
How the Darknet's Free Market Improves Drug Quality
Free-market dynamics on the darknet create a self-regulating environment for commerce. The system operates on principles of supply and demand, where competition among vendors naturally drives quality upward and stabilizes prices. This economic model ensures that only the most reliable and high-quality products succeed, as consumers are empowered to make informed choices.
Encrypted transactions are the foundation of this economy, providing a secure and private method of exchange. This financial privacy allows for a truly free market, unimpeded by external financial oversight. The use of cryptocurrency facilitates these peer-to-peer transactions, ensuring that all economic activity remains confidential and efficient.
Trusted vendor reviews form a critical feedback mechanism, directly influencing market dynamics. A vendor's reputation, built transparently through consistent customer feedback, becomes their most valuable asset. This system of accountability encourages ethical business practices and high standards, as positive reviews directly correlate with commercial success. The darknet market thus evolves into a refined platform where quality and trust are the primary currencies.

How Privacy and Reviews Make the Darknet Drug Trade Safer
Transactional privacy on dark web sites is a foundational element that extends its advantages beyond the marketplace to the individual user. The use of encrypted transactions, primarily through cryptocurrencies, ensures that financial activities are disconnected from personal identities. This creates a protective barrier for all participants, safeguarding them from potential external scrutiny and allowing for personal autonomy over one's choices.
The darknet commerce ecosystem thrives on this principle, supported by a system of trusted vendor reviews. This feedback mechanism provides an objective measure of product quality and vendor reliability, replacing the need for physical inspection. It fosters a self-regulating environment where high standards are maintained through collective user experience, not external enforcement.
This combination of financial anonymity and community-based verification facilitates a secure drug trade where informed decisions can be made. Users can access detailed product listings and assess vendor reputations with a high degree of confidence, knowing their own participation is protected by robust cryptographic protocols. The result is a functional economic model that prioritizes safety, quality, and discretion for everyone involved.